Sir Tim Berners-Lee has launched the Contract for the Web initiative, a set of rules and guidelines designed to save the internet from becoming a "digital dystopia".
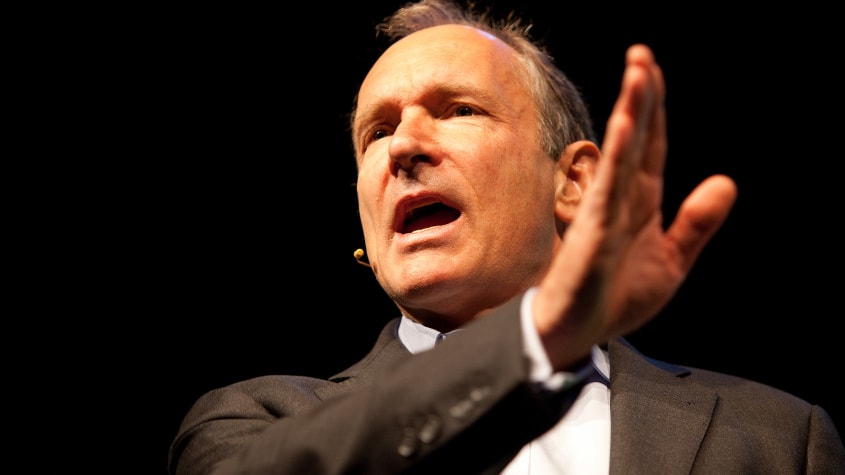
The founder of the World Wide Web said the internet is currently under threat from political manipulation, fake news and privacy violations, adding action must be taken now to save it from irreparable damage.
The Contract for the Web has been drafted over the past year in association with 80 organisations, the final form of which includes nine principles to adhere to, three each for governments, companies and individuals.
In addition to its principles, the Contract for the Web acts somewhat like a badge of honour for companies which back it. More than 150 organisations have given the contract its support and, in turn, have been added to a list of endorsers – a group of verified proponents of a safe and open internet.
To remain on the list of endorsers, companies must be able to consistently demonstrate they are actively implementing and developing solutions to combat the issues threatening the internet.
So far, Google, Facebook, Microsoft, GitHub, Twitter and Reddit are among the most prominent backers. Amazon is a notable absentee.
"I think people's fear of bad things happening on the internet is becoming, justifiably, greater and greater," Berners-Lee told the Guardian. "If we leave the web as it is, there's a very large number of things that will go wrong.
"It's not that we need a 10-year plan for the web, we need to turn the web around now."
It's not clear how the initiative will enforce the rules and whether it will make much impact on the way governments and tech companies do business and conduct themselves on the internet.
It will likely take a big industry push to collectively hold others to account and involve assigning some social capital to those who retain their membership to the Contract for the Web.
According to the principles of the contract, governments are tasked with providing an open internet to the masses and uphold their constituents' rights to online privacy.
The private sector principles state that the internet must be made affordable and accessible to all, that companies must respect privacy and users' personal data, and that technologies should be developed to "support the best in humanity and challenge the worst".
According to the contract, individuals should actively contribute and collaborate on the web, build strong and respectful communities that respect civil discourse and ultimately join the fight for an open internet.
Berners-Lee has been an outspoken voice in the fight for an open internet for years, championing a variety of projects that promote the internet such as the World Wide Web Consortium.
In recent years, Berners-Lee has been heavily critical of the actions of major technology companies on the internet. Speaking at OpenText Enterprise World earlier this year, he said the modern web is like an episode of Black Mirror, a popular Netflix series depicting a dystopian future planet.
The internet luminary has also previously stated that big tech companies such as Facebook and Google are helping to "weaponise the web" due to the amount of control they have on what ideas are shared and hidden.
This latest wave of phishing attacks incorporates real audio recordings to create a sense of urgency.

Cyber criminals are stealing the login credentials of Microsoft Office 365 users using a phishing campaign that tricks victims into believing they've been left voicemail messages.
In the last few weeks, there's been a surge in the number of employees being sent malicious emails that allege they have a missed call and voicemail message, along with a request to login to their Microsoft accounts.
The phishing emails also contain an HTML file, which varies slightly from victim to victim, but the most recent messages observed include a genuine audio recording, researchers with McAfee Labs have discovered.
Users are sent fake emails that inform them of a missed call and a voicemail message
When loaded, this HTML file redirects victims to a phishing website that appears to be virtually identical to the Microsoft login prompt, where details are requested and ultimately stolen.
"What sets this phishing campaign apart from others is the fact that it incorporates audio to create a sense of urgency which, in turn, prompts victims to access the malicious link," said McAfee's senior security researcher Oliver Devane.
"This gives the attacker the upper hand in the social engineering side of this campaign.
This Office 365 campaign has made great efforts to appear legitimate, such as through designing the phishing site to resemble the Microsoft login page. Another trick the cyber scammers use to look real is by prepopulating victims' email addresses into the phishing site and requesting just the password.
The phishing site appears virtually identical to the actual Microsoft login prompt and preloads victims' emails
Users are presented with a successful login message once the password is provided, and are then redirected to the office.com login page.
Researchers found three different phishing kits being used to generate malicious websites, Voicemail Scmpage 2019, Office 365 Information Hollar, and a third unbranded kit without attribution.
The first two kits aim to gather users' email addresses, passwords, their IP addresses and location data. The third kit uses code from a previous malicious kit targeting Adobe users in 2017, the researchers said, and it's likely the old code has been reused by a new group.
A wide range of employees across several industries, from middle management to executive level, have been targeted, although the predominate victims are in the financial and IT services fields. There's also evidence to suggest several high-profile companies have been targeted.
McAfee has recommended as a matter of urgency that all Office 365 users implement two-factor authentication (2FA). Moreover, enterprise users have been urged to block .html and .htm attachments at the email gateway level so this kind of attack doesn't reach the final user.
"We urge all our readers to be vigilant when opening emails and to never open attachments from unknown senders," the researchers added. "We also strongly advise against using the same password for different services and, if a user believes that his/her password is compromised, it is recommended to change it as soon as possible."
The use of audio in this campaign points to a greater tenacity among cyber fraudsters, who are adopting more sophisticated social engineering techniques. For example, earlier this year artificial intelligence (AI) combined with voice technology was used to impersonate a business owner and fool his subordinate into wiring £200,000 to a hacker's bank account.
Most British businesses have suffered a data breach in the past year, with executives saying cyber attacks were becoming more sophisticated.

That's according to a survey of 250 C-level business leaders across the UK by security firm Carbon Black, which said data breaches and hacking attacks were becoming the "new normal".
Of the businesses polled, 84% said they'd suffered a data breach within the last year, with the same number reporting an overall increase in the number of attacks they faced. Larger companies reported a doubling in attack volume, while smaller businesses said attack frequency had increased by 57%. Nine in ten of those surveyed said they believed that attacks were becoming more sophisticated."As we analyse the findings of our third UK Threat Report, it appears businesses are adjusting to the 'new normal' of sustained and sophisticated cyberattacks," said Rick McElroy, head of security strategy at Carbon Black. "Greater awareness of external threats and compliance risks have also prompted businesses to become more proactive about managing cyber risks as they witness the financial and reputational impacts that breaches entail."
Not all data breaches had a financial cost though. The survey revealed about a third of incidents had a financial impact, with only one in ten leading to severe damages. However, three quarters of respondents said they suffered reputational damage.
Three quarters of British business leaders also said they were more confident in their own security abilities – with half saying they feel a little bit more confident, and 29% saying they felt a lot more confident – while nine out of ten business leaders surveyed reported they planned to increase their security budgets in the coming year.
"As the cyber defence sector continues to mature, businesses are becoming more aware of the tools at their disposal and the tactics they can use to combat cyberattacks," said McElroy. "We believe this growing confidence is indicative of a power shift in favour of defenders, who are taking a more proactive approach to hunting out and neutralising threats than previously."
He pointed to the use of proactive threat hunting to stop attacks before they start, with 75% of companies saying they'd spotted attack activity using such techniques that likely would have gone unnoticed previously.
Custom malware is the most frequent form of attack, though Carbon Black also reported a rise in phishing attacks against companies – and they're the vector that causes the highest number of successful breaches, according to the survey. Carbon Black said that phishing trend suggests hackers are still targeting users as the weakest link.
That makes it no surprise that a quarter of CIOs would like a bigger team to battle the security threat, but it could prove a challenge with more than half of companies surveyed saying that recruiting and training specialist security staff is harder this year than last.
TfL want more details from the taxi-hailing firm before any future decision is made.

Transport for London has announced it will only grant Uber a two-month private hire operator licence instead of the five-year licence the company sought.
The two-month licence comes with "new conditions to ensure passenger safety" as TfL said it wanted more details from Uber.
Last year, the chief magistrate issued a 15-moth private hire licence to Uber, which is due to end on 25 September at 23:59.
Within its two-month licence, TfL will consider any future licensing decision based on additional information Uber provides.
"Uber London Limited has been granted a two-month private hire operator licence to allow for scrutiny of additional information that we are requesting ahead of consideration of any potential further licensing application," a TfL spokesperson said.
The root of the issue goes back to 2017 when TfL originally denied a licence renewal for Uber. The capital's transport organisation posted a statement on Twitter stating that Uber was "not fit and proper to hold a private hire operator licence".
TfL said that Uber's approach and conduct "demonstrate a lack of corporate responsibility" and listed four other areas of fault, including Uber's failure to report serious criminal offences, its approach to medical certificates and its approach to how DBS checks are obtained.
The impasse was eventually broken in court when the chief magistrate granted Uber a 15-month licence but ordered a number of extra conditions to be attached. Uber was required to produce independently verified reports every six months, add three non-executive members to its board and to maintain arrangements with the Met Police for the reporting of passenger complaints.
These conditions will remain for the new two-month licence, but there will be additional conditions covering ride-sharing, appropriate insurance and driver document checks by Uber.
When it comes to ransomware, it only takes one person to let the marauders run free.

That's the assessment of cybersecurity company Malwarebytes, which has found as many as one third of small-to-medium-sized businesses were hit by ransomware last year, and that "the human factor" is increasingly behind large-scale outages. The findings come as part of Malwarebytes' Second Annual State of Ransomware Report, which showed that, of the 32 percent of companies hit by at least one malware attack last year, one fifth had to completely stop operations immediately. Do not pass go, do not collect $200 (unless you're coughing it up in Bitcoin). The figures paint a grim picture of digital security in the modern era, at a time when malware attacks routinely make news headlines, and ransomware (malicious software that infects systems and demands a ransom to regain access to encrypted files) has the power to bring everyth
Just because a malware outbreak has begun to fade away from the newspaper headlines, doesn’t mean your troubles are over. Many firms can continue to suffer long afterwards. Here’s a salutary reminder for all businesses, my thanks to Graham Cluley.

Just because a malware outbreak has begun to fade away from the newspaper headlines, doesn’t mean your troubles are over. Many firms can continue to suffer long afterwards. In late June, a malware attack crippled businesses and critical infrastructure in Ukraine at astonishing speed. Initially suspected of being a similar ransomware attack to the WannaCry outbreak seen the month before, the malware (variously named as Petya, NotPetya or GoldenEye by security vendors) appears to have been launched through a malicious automatic update to a popular Ukrainian accounting software tool called MeDoc. We tell companies all the time to keep their software updated with the latest available patches, and yet here was an update which actually delivered a devastating malware attack. The irony isn’t lost on anybody. Once in place on an infected PC, the malware would spread to other networked computers, using a variety of lateral movement techniques. And it didn’t take long for GoldenEye to spread beyond Ukraine’s borders, hitting the of offices of multinational companies in the United States, UK, Russia, France, Germany and elsewhere.
To find out more about how we can resolve your IT issues please email or call us:
Send us an email Call us +44 (0)1462 416400









